Auto-approve workflow action
When GitHub disabled automatic workflow runs to prevent crypto miners it made some OSS maintainers lives harder, so I wrote a GitHub Action that automatically approves all pending workflow runs (so long as they don't edit .github/workflows)
| Fact Sheet | |
|---|---|
| Author | mheap |
| Contributors | 2 |
| Stars | 6 |
| Repo | https://github.com/mheap/automatic-approve-action |
| Marketplace | https://github.com/marketplace/actions/automatic-approve |
What does it do?
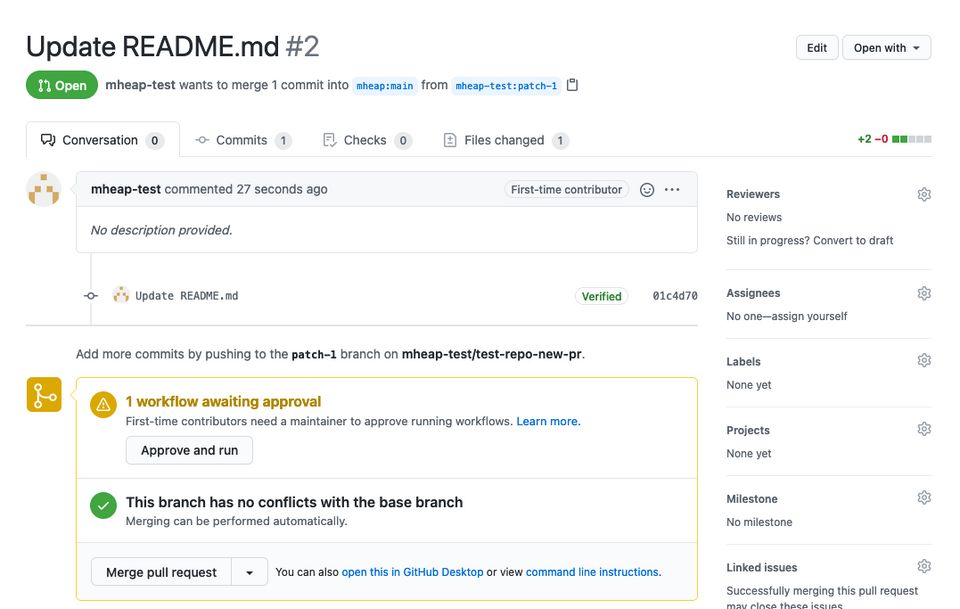
When a pull request is raised by a first time contributor to a repo, the any workflows that would usually be triggered are set to pending. This is to prevent bad actors abusing actions for things like crypto mining.
This is a good thing in general, but it affects all pull requests, not just those that change executables. This was the fastest way to fix the issue as any code that executes could be used to start a mining process.
However, it also impacted projects such as the OctoPrint plugin repository which are primarily non-executable metadata.
This action is intended to run every 5 minutes and approve any pending workflow runs, allowing the maintainer to see all the information they need to review a PR such as linting and tests without having to wait for a build to run.
How does it work?
This action runs on a schedule, fetching any pending workflow runs and automatically approving them if some constraints are met. It requires a personal access token as shown in the GitHub API docs.
Working through the action:
- Read a Personal Access Token from the
tokeninput - Create a list of allowed workflows to be automatically approved
- Create a list of dangerous files and automatically add
.github/workflowsto it - Fetch the list of workflow runs with a status of
action_requiredin the current repository - Filter down the list of pending workflows to those which exist in the list of allowed workflows
- Remove any runs that edit a file that is in the
dangerous_fileslist - Finally, approve any runs that are left in the list. These are runs that have an action of
status_required, are listed in theworkflowsinput and do not change any files indangerous_files.
Common use cases
There's only one use case for this action, which is to approve safe workflows to run automatically. This typically involves running processes such as linting or static site generation.
yaml